A critical vulnerability with the Zoom client for windows allows attackers to steal Windows login credentials.
Zoom is an online video communication platform that has features such as video conferencing, online meetings, chat, and mobile collaboration.
Zoom usability is high now as most of the organization has been closed and the employees are provided with options to work from home.
Zoom Vulnerability
Zoom client for Windows supports for Universal Naming Convention (UNC), which is the feature that converts the URLs sent in the chat into hyperlinks.
So if the user click’s on the link it will open that with the default browser, but the problem resides in how the Zoom handles URLs.
A security researcher who goes by Twitter handles Mitch (@_g0dmode) discovered that Zoom client also converts the Windows networking UNC paths into a clickable URL.
If someone click’s on the UNC path URL then Windows will try to establish a connection with the remote site and windows will send the user’s login name and their NTLM password hash, by using the tools like John the Ripper, Rainbow, Hashcat crack attackers can capture the login credentials.
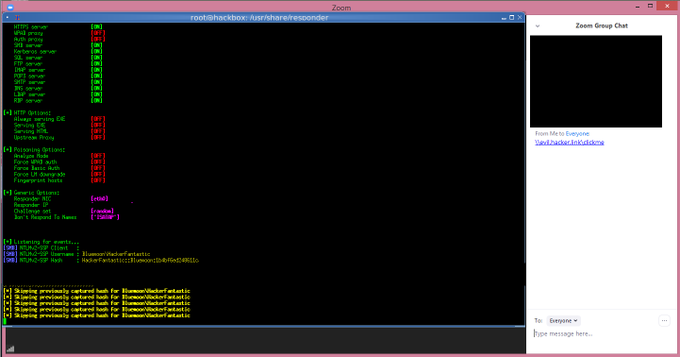
Further, a security researcher with handle Matthew Hickey (@HackerFantastic) checked the attack method and able to obtain NTLM password hashes exploiting the vulnerability.
Also, Hickey told that an attacker could exploit UNC path injection to run arbitrary code on the windows machine.
Former NSA hacker Patrick Wardle discovered two zero-days, that could be launched by a local attacker who has physical control over the machine.
Reference : https://gbhackers.com/zoom-vulnerability/